Interconnected technologies are the growing network of devices, systems and applications connected to the internet and each other. They transform enterprises, enabling them to gather more data and automate processes. But they also bring new risks and challenges when securing business assets and safeguarding customers.
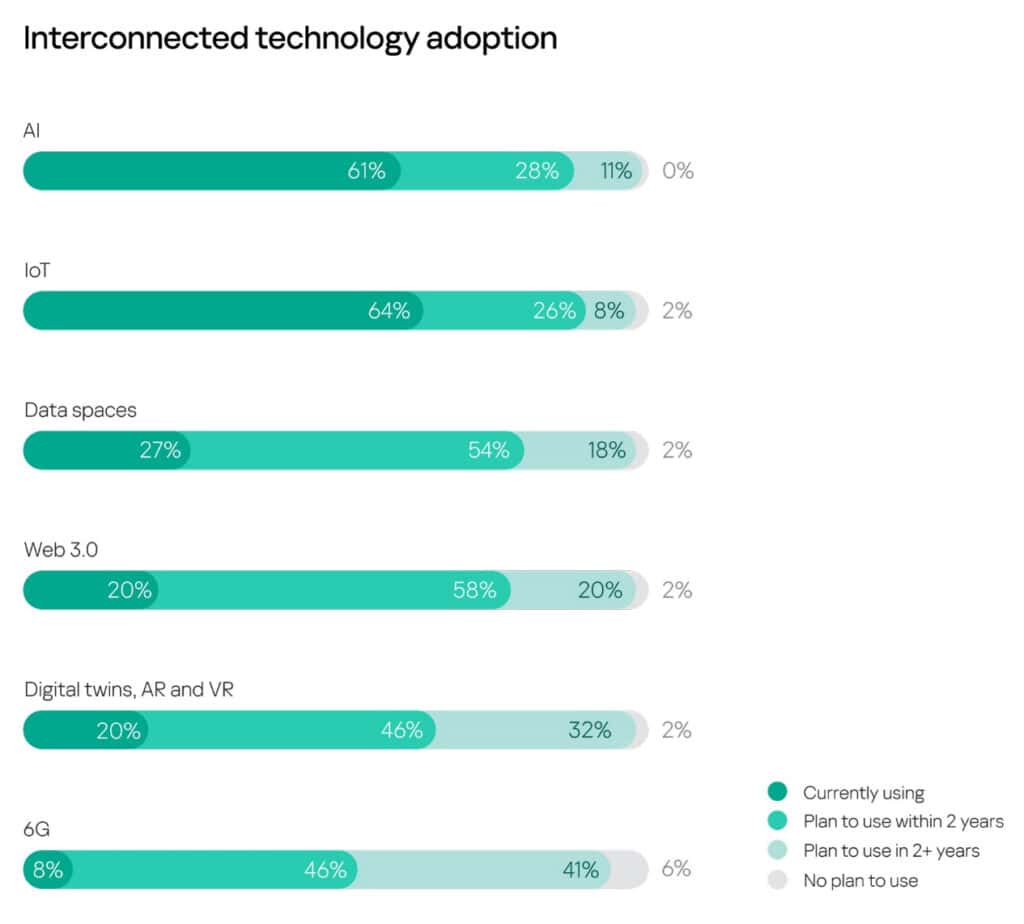
A recent Kaspersky study found that AI and IoT are already used by 61% and 64% of companies respectively, while 28% and 26% of companies plans to adopt them within two years. Data spaces are used by 27% of businesses, with more than half (54%) intending to adopt them soon.
Other interconnected technologies (digital twins, AR, VR, web 3.0, 6G), are used by 8-20% of companies participating in the survey, but more than 70% are considering integrating them into their business processes soon.
The expanding use of AI and IoT has the potential to expose organisations to new vulnerabilities. According to the research, 13-14% of organisations from the region think AI and IoT are ‘very difficult’ or ‘extremely difficult’ to protect, while only 6% of the AI users and 10% of the IoT owners believe their companies are fully protected.

According to Adrian Hia, managing director for Asia Pacific at Kaspersky, “Undoubtedly, new technological tools play a vital role in improving the efficiencies and productivity of enterprises in the region. However, there are loopholes, particularly in cybersecurity, that need to be addressed. Our recent study showed more than half of the companies are using AI and IoT in their organisations, but 21% of them think AI and IoT are somewhat difficult to protect. It shows that there is a skills and knowledge gap that needs to be patched with urgency.”
Recommendations going forward
Given the scale of change that interconnected technologies is likely to bring, organisations must develop a strategy to implement and protect them. Kaspersky recommends four effective ways to ensure organisations are prepared to protect interconnected technologies:
Adopt secure-by-design principles. By integrating cybersecurity into each stage of the software development lifecycle, secure-by-design software and hardware become resilient against cyberattacks, contributing to the overall security of digital systems. Cyber Immune solutions based on KasperskyOS, for instance, allow companies to minimize the threat surface and significantly decrease the ability of cybercriminals to perform a successful attack.
Train and upskill your workforce. Building a cyber-aware culture requires a comprehensive strategy that empowers employees to gain knowledge and put it into practice. With Kaspersky Expert training, InfoSec professionals can advance their skills and defend their companies against attacks.
Upgrade your cybersecurity solutions and use centralized and automated platforms such as Kaspersky Extended Detection and Response (XDR). As companies adopt interconnected technologies, they need cybersecurity solutions with more advanced features, enabling them to collect and correlate telemetry from multiple sources and provide effective threat detection and rapid automated response.
As many AI solutions are built on containers, it’s important to secure the infrastructure they are integrated in with cybersecurity products – such as Kaspersky Container Security – that allows companies to detect security issues at every stage of the app lifecycle, from development to operation.
Meet regulations to avoid legal problems or reputational damage, by ensuring your cybersecurity practice meets changing standards and legal requirements.



